In this post, I will provide a detailed, step-by-step guide to conducting a cloud security configuration review. We will cover the importance of configuration reviews, best practices for ensuring the security of your cloud environment, and tools and techniques that you can use to identify and address potential vulnerabilities or misconfigurations. Whether you are new to cloud security or an experienced professional, this guide will provide you with the knowledge and skills you need to confidently conduct a comprehensive configuration review and maintain a secure cloud environment.
As an example, we will be focusing on the AWS cloud for this blog post to illustrate the various steps and considerations involved in conducting a cloud security configuration review.
What is Cloud Security
Cloud security is a critical concern for organizations using cloud platforms such as Amazon Web Services (AWS) or Microsoft Azure, Google Cloud Platform (GCP), and other Cloud Platforms. These platforms provide a range of security measures to help protect data and applications, including access controls, network security, and data protection. However, it is important for organizations to also implement their own security measures and perform regular reviews to ensure that their cloud configurations are secure. This can include setting up multi-factor authentication, implementing encryption, and regularly updating security policies and controls. By taking a proactive approach to cloud security, organizations can ensure that their data and applications are protected in the cloud and comply with relevant laws and regulations.
Overall, AWS, Azure, and GCP offer comprehensive security measures to help protect data and applications in the cloud. It is important for organizations using these platforms to regularly review and update their security configuration to ensure that it remains effective at protecting against potential threats.
Why Companies should do a cloud security configuration review
Cloud security configuration reviews are crucial for companies to ensure that their data and systems are protected from potential security threats. These reviews allow companies to identify any vulnerabilities in their cloud systems and take the necessary steps to address them before they can be exploited by cybercriminals.
Additionally, regular cloud security configuration reviews can help companies stay compliant with industry regulations and standards, such as the Payment Card Industry Data Security Standard (PCI DSS) and the Health Insurance Portability and Accountability Act (HIPAA). By conducting these reviews, companies can also minimize the risk of data breaches and protect their reputation and brand trust. Overall, investing in cloud security configuration reviews is a smart business decision that can help companies ensure the security of their sensitive data and systems.
Perquisites before starting the security review
To ensure the success of a cloud security review, it’s important to have all necessary prerequisites in place. This includes assembling the review team, gathering relevant documentation, identifying the scope of the review, and gathering the appropriate Credentials. By preparing in advance, you can ensure that the review is comprehensive and effective at identifying and addressing any potential vulnerabilities or threats to your cloud environment.
Involve the appropriate stakeholders
This means ensuring that the people who are responsible for the security of the AWS environment are involved in the review process. This could include security professionals, such as security engineers or administrators, as well as application owners and network administrators.
Involving these stakeholders is important for several reasons. First, it ensures that all relevant parties are aware of the review and can provide input or feedback. This can help to identify any potential risks or vulnerabilities that might have been missed by the review team. Second, involving the appropriate stakeholders allows for a more comprehensive review of the security configuration. Security professionals can provide insight into best practices and identify any potential weaknesses in the configuration, while application owners and network administrators can provide a deeper understanding of how the system is used and how it is configured.
Gather relevant documentation
This includes any documents that provide information about the current security posture of the AWS environment, such as security policies and procedures, network diagrams, and access control lists.
Having this documentation on hand can be helpful in understanding the current security posture and identifying any potential vulnerabilities or areas for improvement. It can also provide context for the review process and help to ensure that all relevant aspects of the security configuration are considered.
Credentials to access AWS Environment
If you want to perform a security configuration review on your Amazon Web Services (AWS) account, you will need two things: access keys and an AWS account with a security auditor role. Access keys are unique combinations of a user-defined access key ID and a secret access key that are used to sign programmatic requests made to AWS. They allow you to authenticate your identity and access AWS resources. In addition, AWS access keys are also required to run the automated tools.
On the other hand, the security auditor role is a special type of AWS Identity and Access Management (IAM) role that grants permissions to perform security-related tasks on your AWS account. This includes reviewing security configurations, identifying vulnerabilities, and implementing security best practices.
Identify the Scope of the review
This involves determining which resources within the AWS environment will be included in the review. These resources could include Elastic Compute Cloud (EC2) instances, Simple Storage Service (S3) buckets, Relational Database Service (RDS) databases, and any other assets that are relevant to the review.
It is essential to clearly define the scope of the review before proceeding, as this will help ensure that all relevant assets are included and that the review is comprehensive. It will also help to ensure that the review is focused and efficient, as it will allow you to prioritize the assets that are most important to the organization.
List Deployed Resources using Tag Editor
To extract a list of all AWS resources deployed in an AWS environment, the AWS Tag Editor can be used. The following steps can be followed to do so:
- Sign in to the AWS Management Console.
- Navigate to the Tag Editor in the resource groups section of the AWS Management Console.
- In the “Regions” dropdown menu, select the region you want to list. [Recommended: All regions]
- In the “Resource type” dropdown menu, select the type of resources you want to list. [Recommended: All supported resource types]
- In the Filter by tag field, enter the name and value of the tag that you want to use to filter the resources. [Recommended: Leave the fields empty]
- Click the “Search resources” button to view the resources that match the specified selection.
- To view the details of a resource, click on the resource in the list.
- Click on the “Export resources to CSV” dropdown menu and select “Export all tags”.
- Now the “resources.csv” file will be downloaded to your local machine.
The CSV file generated by the Tag Editor can be used to locate the deployed resources in your AWS account and navigate to specific regions and resource types for the cloud security review. The file will contain a list of the resources, their resource IDs, resource types, and region, as well as any tags that have been applied to the resources. This information can be helpful in identifying the resources that are relevant to your review and locating them in the AWS Management Console.

Manual Cloud Security Configuration Review
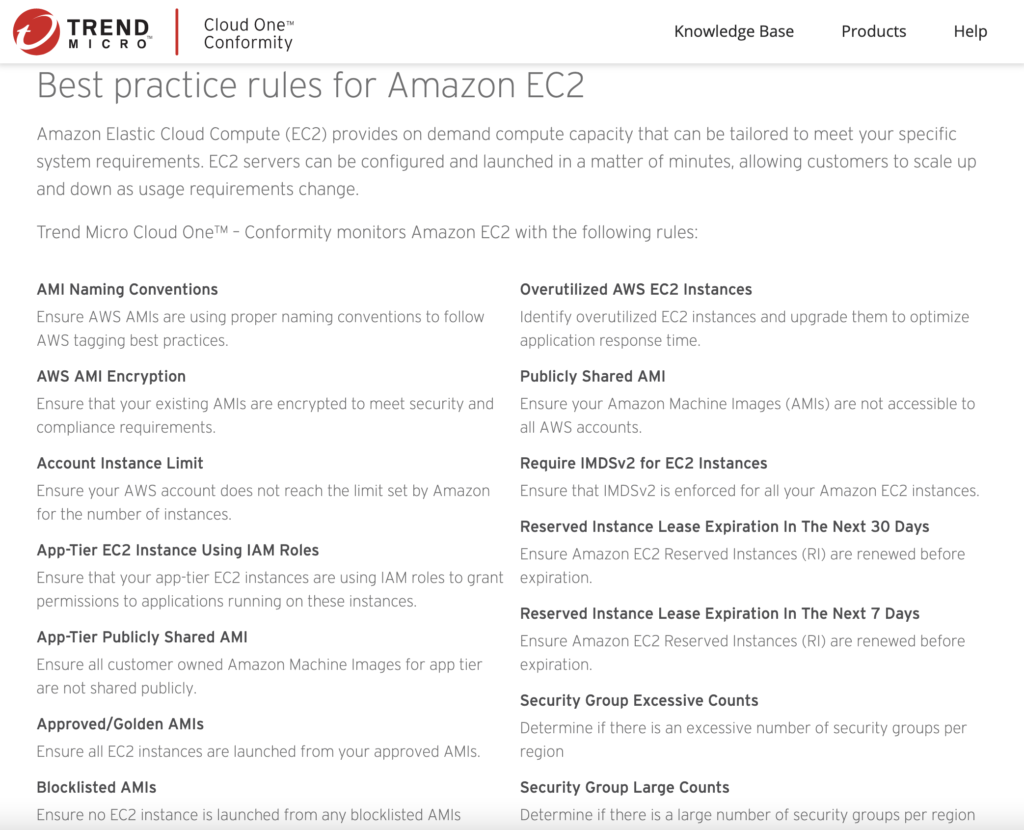
By manually reviewing your cloud configurations against established best practices and standards, you can identify any potential vulnerabilities or misconfigurations that could leave your data and resources at risk. Trend Micro’s knowledge base can provide helpful guidance and recommendations for securing your cloud environment, while the CIS benchmarks offer a set of best practices and guidelines for configuring and securing various cloud platforms. By leveraging these resources, you can thoroughly review your cloud security configuration and make any necessary adjustments to strengthen your security posture.
Trend Micro | Cloud One Conformity
Whether you’re just getting started with cloud computing or have been using it for years, trend one conformity can help you improve your security posture. The knowledge base is regularly updated with the latest information, so you can be confident that you have the most up-to-date guidance for your security review.
“Trend Micro’s trend one conformity knowledge base offers a comprehensive set of guidelines for manual security reviews of cloud platforms like AWS, Azure, and GCP. These rules provide a framework for evaluating the security of your cloud infrastructure and identifying potential vulnerabilities. With trend one conformity, you can ensure that your cloud platform is compliant with industry standards and best practices.
By following the rules in trend one conformity, you can ensure that your cloud platform is secure and compliant. This can give you peace of mind and help you avoid costly security breaches. Whether you’re using AWS, Azure, or GCP, trend one conformity can help you secure your cloud infrastructure and protect your business.”
Conformity Knowledge Base: https://www.trendmicro.com/cloudoneconformity/knowledge-base/
CIS Benchmarks
The CIS (Center for Internet Security) benchmarks are a set of guidelines that provide recommendations for secure configuration of systems, networks, and applications. These guidelines can be used as a reference when conducting a cloud security configuration review to help ensure that your cloud environment is properly secured.
Some key CIS benchmarks for cloud security configuration review include:
- CIS AWS Foundations Benchmark: This benchmark provides guidelines for securing Amazon Web Services (AWS) environments, including recommendations for identity and access management, network security, and data protection.
- CIS Microsoft Azure Foundations Benchmark: This benchmark provides guidelines for securing Microsoft Azure environments, including recommendations for identity and access management, network security, and data protection.
- CIS Google Cloud Platform Foundations Benchmark: This benchmark provides guidelines for securing Google Cloud Platform (GCP) environments, including recommendations for identity and access management, network security, and data protection.
By following the CIS benchmarks for cloud security configuration review, organizations can better protect their resources and data in the cloud. It is important to regularly review and update your cloud security configuration to ensure that it remains effective at protecting your resources and data.
CIS Benchmarks: https://www.cisecurity.org/cis-benchmarks/

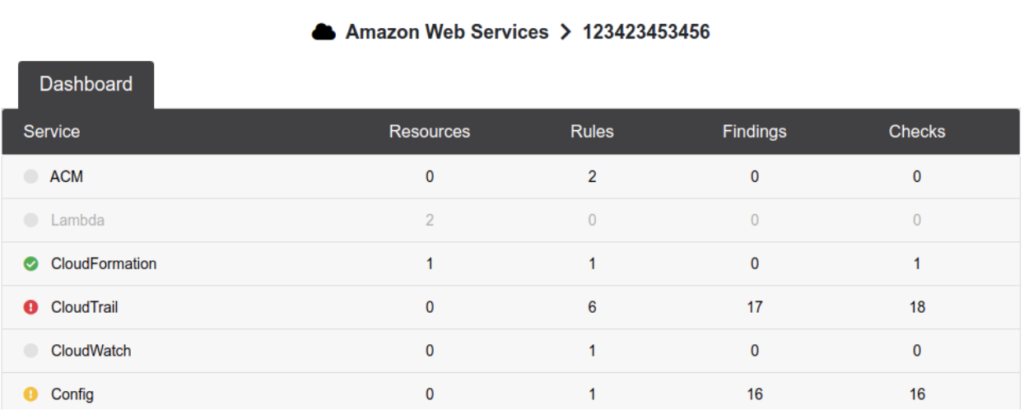
Automated Tools
Automated tools such as Scout Suite and Cloudsploit can be extremely useful for conducting automated cloud security configuration reviews. These tools can scan your cloud environment and identify potential vulnerabilities or misconfigurations that may be present.
By using automated tools like Scout Suite and Cloudsploit, you can save time and resources while still maintaining a high level of security in your cloud environment. It’s important to note, however, that automated tools should be used in conjunction with manual review processes to ensure the thoroughness and accuracy of your security review.
Scout Suite
ScoutSuite is an open-source tool that helps organizations assess and secure their cloud infrastructure. It is designed to be used with Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP). With ScoutSuite, users can perform a comprehensive security audit of their cloud environment. The tool provides a detailed report of any vulnerabilities or misconfigurations, along with recommendations for how to address them.
Overall, ScoutSuite is a powerful and useful tool for anyone looking to secure their cloud infrastructure. It is an essential tool for organizations of all sizes and is highly recommended for anyone looking to protect their data and resources in the cloud.
ScotSuite: https://github.com/nccgroup/ScoutSuite
CloudSploit
CloudSploit by Aqua is a cloud security monitoring and management platform that helps organizations protect their cloud infrastructure from threats and vulnerabilities. With CloudSploit, users can continuously monitor their cloud resources for security issues and receive real-time alerts when potential risks are detected.
Overall, CloudSploit by Aqua is a powerful and reliable tool for ensuring the security of your cloud infrastructure. With its comprehensive security checks and easy-to-use interface, it is an essential tool for any organization looking to protect their cloud resources.
CloudSploit: https://github.com/aquasecurity/cloudsploit

Security Certifications
Cloud certifications are professional qualifications that demonstrate a person’s knowledge and skills in cloud computing and related technologies. There are several different cloud certifications that individuals can pursue to gain expertise in cloud security configuration. Some of the most popular options include:
AWS Certified Security – Specialty
This certification covers a wide range of security-related topics, including identity and access management, data protection, and compliance. It is designed for professionals who have a deep understanding of AWS security capabilities.
Azure Security Engineer Associate
This certification is designed for professionals who implement, monitor, and maintain security in Azure environments. It covers topics such as identity and access management, data protection, and network security.
Professional Cloud Security Engineer
This certification is designed for professionals who design, develop, and manage secure infrastructure on GCP. It covers topics such as identity and access management, data protection, and network security.
Conclusion
In conclusion, a comprehensive cloud security configuration review is essential for any organization that relies on cloud computing. By following the guidelines outlined in this guide, businesses can ensure that their data is protected against potential security breaches and maintain a secure cloud environment. It is important to regularly review and update your security configuration to stay up-to-date with the latest threats and best practices. Investing in the security of your cloud infrastructure is crucial for the success and protection of your business.