Web applications are a crucial part of today’s online landscape, with businesses relying on them to provide services to their customers. However, as the use of web applications increases, so does the risk of cyber attacks. Threat modeling is a technique that can help organizations identify potential security threats and vulnerabilities in their web applications. In this blog post, we will explore the concept of threat modeling, its importance for web applications, and the benefits it offers. We will also take a closer look at the threat modeling process, the types of threats that web applications face, the various threat modeling techniques and tools available, and best practices for effective threat modeling. So, let’s dive in!
Introduction to Threat Modeling
Web applications are increasingly becoming a popular platform for businesses and organizations to deliver their services and interact with customers. However, with this increase in usage comes an increase in risk, as web applications are often the target of cyber attacks. Threat modeling is a process of identifying potential threats and vulnerabilities in a system or application and taking steps to mitigate them. It is an important part of the overall security posture of a web application and can help ensure that the application is protected against a range of cyber threats.
What is threat modeling?
Threat modeling is the process of identifying, prioritizing, and mitigating potential threats and vulnerabilities in a system or application. It involves thinking about how an attacker might try to exploit weaknesses in the application’s design, code, or infrastructure, and then taking steps to prevent those attacks from succeeding.
Why is threat modeling important for web applications?
Threat modeling is important for web applications because they are often exposed to a range of cyber threats, including injection attacks, cross-site scripting, and data breaches. By identifying potential threats and vulnerabilities early in the development process, developers can take steps to prevent those attacks from succeeding, reducing the risk of a successful cyber attack.
What are the benefits of threat modeling?
There are several benefits of threat modeling, including:
- Improved security: By identifying potential threats and vulnerabilities early in the development process, developers can take steps to prevent those attacks from succeeding, reducing the risk of a successful cyber attack.
- Reduced costs: Fixing security vulnerabilities later in the development process can be much more costly than addressing them during the design phase.
- Better understanding of the system: Threat modeling can help developers and security engineers to gain a better understanding of how their application works and how it might be attacked.
- Compliance: Many industry standards and regulations, such as PCI-DSS and HIPAA, require organizations to perform regular threat modeling exercises to ensure the security of their systems.
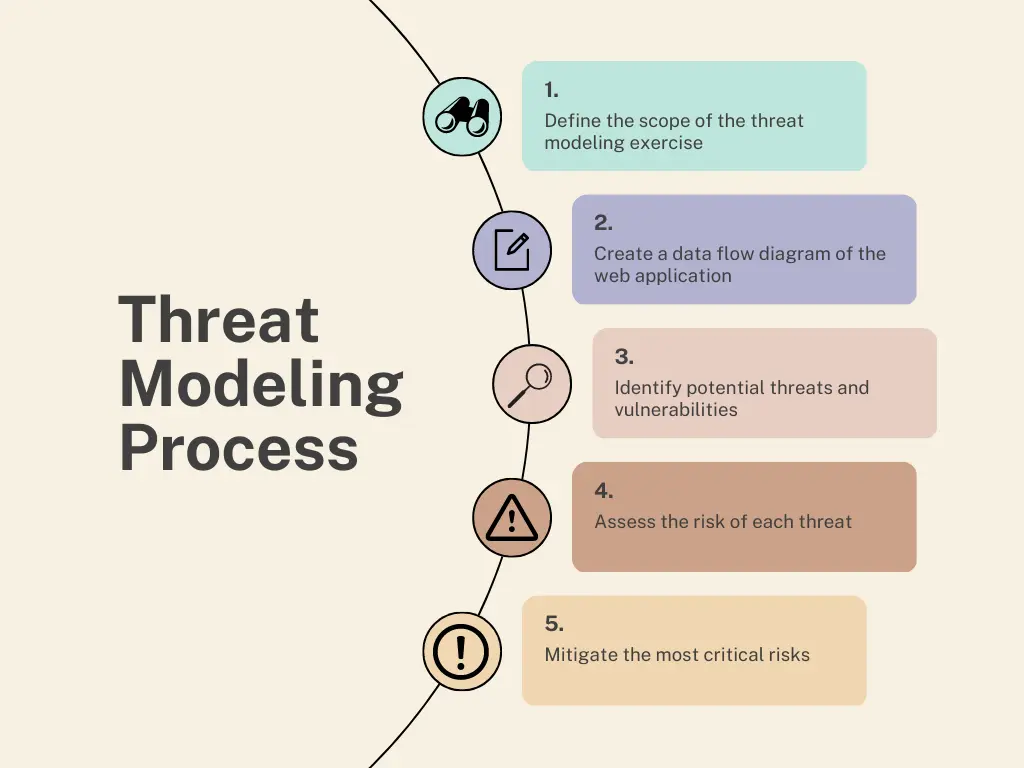
The Threat Modeling Process
Define the scope of the threat modeling exercise
- Identify the web application or feature that you want to model.
- Determine the level of detail you need to model based on the complexity and criticality of the application or feature.
- Identify the stakeholders who should be involved in the threat modeling exercise, including developers, architects, testers, and security experts.
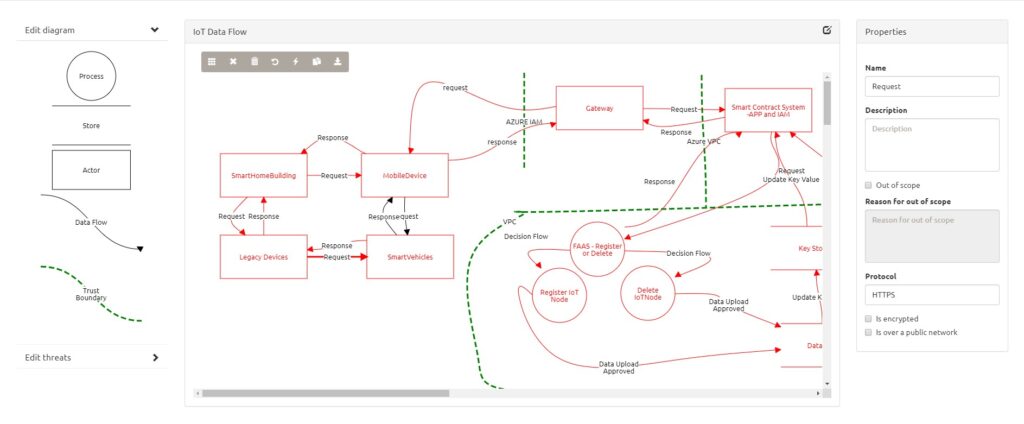
Create a data flow diagram of the web application:
- A data flow diagram (DFD) is a visual representation of the data flow and processes within the web application.
- Identify the major components of the web application, including users, web servers, application servers, databases, and external systems.
- Draw arrows to show how data flows between the components.
- Use different symbols to represent the different types of data, such as user input, output, and stored data.
Identify potential threats and vulnerabilities:
- Use the DFD to identify potential threats and vulnerabilities in the web application.
- Consider both internal and external threats, including human errors, software bugs, and malicious attacks.
- Use threat modeling techniques, such as STRIDE or PASTA, to identify potential threats and vulnerabilities.
- Document the threats and vulnerabilities in a threat model.
Assess the risk of each threat:
- Determine the likelihood and impact of each threat to the web application.
- Assign a risk score to each threat based on its likelihood and impact.
- Prioritize the threats based on the risk scores, focusing on the most critical risks first.
Mitigate the most critical risks:
- Identify the mitigation strategies for the most critical risks.
- Prioritize the mitigation strategies based on their effectiveness and cost.
- Implement the mitigation strategies in the web application.
- Test the effectiveness of the mitigation strategies.
By following these five steps, you can effectively model the threats to your web application and develop a plan to mitigate the most critical risks. Keep in mind that threat modeling is an iterative process, and you may need to revisit and update your threat model as the web application evolves or new threats emerge.
Types of Threats to Web Applications
When it comes to web application security, there are many different types of threats that can compromise the integrity, confidentiality, and availability of data. Here are some of the most common types of threats to be aware of:
| Attack Categories | Types of Threats to Web Applications | Description |
| Injection attacks | SQL Injection | SQL injection is a type of injection attack that exploits vulnerabilities in web applications that use SQL databases. Attackers can use SQL injection to gain access to sensitive data, modify or delete data, or execute malicious code on the server. |
| Cross-site scripting (XSS) | Cross-site scripting is a type of injection attack that allows an attacker to inject malicious code into a web page viewed by other users. This can be used to steal user credentials, redirect users to malicious websites, or perform other malicious actions. | |
| Authentication and authorization vulnerabilities | Brute force attacks | Brute force attacks are a type of attack where an attacker tries to guess a user’s password by trying many different combinations of characters. This can be made easier if the web application does not have protections in place to prevent automated login attempts. |
| Session hijacking | Session hijacking occurs when an attacker gains access to a user’s session ID and uses it to impersonate the user. This can allow the attacker to gain access to sensitive data or perform actions on behalf of the user. | |
| Data breaches and theft | Insecure storage of data | If data is stored in an unencrypted or easily decryptable format, an attacker may be able to access it by bypassing security measures. |
| Man-in-the-middle attacks | Man-in-the-middle attacks occur when an attacker intercepts communication between a user and a web application. This can allow the attacker to steal sensitive data or modify data in transit. | |
| Denial-of-service attacks | Distributed denial-of-service (DDoS) attacks | DDoS attacks occur when multiple attackers coordinate to send traffic to a single web application at the same time. This can make it difficult for the web application to handle the traffic and can lead to it becoming unavailable. |
| Misconfigured security settings | Lack of encryption | If a web application does not encrypt sensitive data in transit, it may be vulnerable to interception and theft. |
| Excessive permissions | If a web application gives users excessive permissions, they may be able to access data or perform actions that they should not have access to. |
Threat Modeling Techniques
There are several threat modeling techniques that can be used to identify and assess the potential threats and vulnerabilities in a web application. Some of the most commonly used techniques include:
STRIDE
The STRIDE threat model is a popular technique that was developed by Microsoft. It helps to identify potential threats by focusing on six categories of threats:
- Spoofing: where an attacker impersonates a legitimate user or system to gain unauthorized access.
- Tampering: where an attacker modifies data or code to change the behavior of the system.
- Repudiation: where an attacker can deny that an action was taken, making it difficult to trace.
- Information disclosure: where an attacker can gain access to confidential or sensitive information.
- Denial of service: where an attacker can disrupt the availability or performance of the system.
- Elevation of privilege: where an attacker can gain higher-level permissions or access than they are authorized for.
PASTA
PASTA (Process for Attack Simulation and Threat Analysis) is a risk-centric approach to threat modeling. It focuses on identifying the most likely threats and simulating attacks to assess the potential impact of those threats. The PASTA model involves the following steps:
- Preparation: Define the scope of the threat modeling exercise and assemble the team.
- Threat Assessment: Identify and rank the most likely threats and vulnerabilities.
- Attack Simulation: Simulate attacks to determine the impact and effectiveness of each threat.
- Vulnerability Mitigation: Develop and implement strategies to mitigate the most critical risks.
- Results Communication: Document the results of the threat modeling exercise and communicate them to stakeholders.
Trike
The Trike threat model (Threats, Risks, Countermeasures and Knowledgebase) is a comprehensive approach that incorporates multiple threat modeling techniques. It involves the following steps:
- Scope Definition: Define the scope of the threat modeling exercise and identify the assets and resources to be protected.
- Asset Modeling: Develop a model of the web application, including its architecture and components.
- Threat Identification: Identify potential threats to the web application.
- Risk Assessment: Assess the likelihood and potential impact of each threat.
- Countermeasure Selection: Identify and prioritize countermeasures to mitigate the most critical risks.
- Knowledgebase Development: Develop a knowledgebase of threats, risks, and countermeasures to inform future threat modeling exercises.
Using a threat modeling technique can help to identify and assess potential threats to a web application, and develop effective strategies to mitigate those risks. Choosing the most appropriate technique depends on the specific needs and requirements of the web application and the organization behind it.
Threat Modeling Tools
Threat modeling is a complex process that involves identifying potential security risks and vulnerabilities in a web application. Fortunately, there are many tools available that can help streamline the threat modeling process and ensure that all potential risks are identified and addressed. We’ll take a closer look at some of the most popular threat modeling tools available today.
Microsoft Threat Modeling Tool
The Microsoft Threat Modeling Tool is a free tool that is widely used in the industry for threat modeling. This tool allows you to create data flow diagrams of your web application and identify potential threats and vulnerabilities. You can then assign a risk level to each threat and prioritize them based on their impact on your application. The tool also provides recommendations for mitigating each risk.

OWASP Threat Dragon
OWASP Threat Dragon is an open-source tool that is designed to help organizations create and manage threat models for web applications. This tool allows you to create data flow diagrams and identify potential threats and vulnerabilities. You can then assign a risk level to each threat and prioritize them based on their impact on your application. The tool also provides recommendations for mitigating each risk.
ThreatModeler
ThreatModeler is a comprehensive threat modeling tool that allows you to create data flow diagrams and identify potential threats and vulnerabilities. This tool also provides recommendations for mitigating each risk and allows you to track your progress in addressing each risk over time. One unique feature of ThreatModeler is that it includes a library of pre-built threat models that you can use as a starting point for your own threat models.

These are just a few of the many threat modeling tools available today. Each tool has its own unique features and benefits, so it’s important to choose the tool that best meets your organization’s needs. Remember, the tool is just one part of the threat modeling process, and it’s important to involve all stakeholders and keep your threat models up to date to ensure the ongoing security of your web application.
Best Practices for Effective Threat Modeling
Threat modeling can be a powerful tool to improve the security of your web application. However, to get the most out of your threat modeling exercise, there are some best practices that you should follow. Here are some key considerations:
Involve all stakeholders
It’s essential to involve all stakeholders in the threat modeling process. This includes developers, architects, business analysts, and security experts. Everyone should be familiar with the web application’s functionality, business logic, and potential security risks. Having diverse perspectives can help identify vulnerabilities that may have been overlooked by others.
Keep threat models up to date
Threats to your web application can change over time, so it’s important to keep your threat models up to date. This means reviewing and updating them regularly, especially after significant changes to the application, such as adding new features or functionality.
Prioritize risks based on impact and likelihood
After identifying potential threats, it’s crucial to prioritize them based on their impact and likelihood. Risks that have a high impact and likelihood should be addressed first. This will ensure that you’re mitigating the most critical risks and reducing the overall risk to your web application.
Integrate threat modeling into the development process
Threat modeling should be integrated into the development process, so it’s not viewed as an additional task but as an essential part of building secure software. This means incorporating threat modeling into the development lifecycle, such as including it in design reviews, code reviews, and testing.
Use the right threat modeling technique and tool
Using the right threat modeling technique and tool can make a significant difference in the effectiveness of your threat modeling exercise. Choose a technique that aligns with your web application’s complexity and your team’s expertise. Similarly, select a tool that provides the features and capabilities you need to create and manage your threat models.
Ensure a collaborative and iterative approach
Threat modeling should be a collaborative and iterative process. Each stakeholder should have an opportunity to contribute and provide feedback throughout the exercise. Additionally, as new information becomes available, such as new vulnerabilities or changes to the web application, the threat models should be updated and re-evaluated.
By following these best practices, you can ensure that your threat modeling exercise is effective and contributes to the overall security of your web application.
Conclusion
Threat modeling is essential for identifying and mitigating security risks in web applications. Developers can follow a structured approach and be aware of common vulnerabilities, such as injection attacks and authentication flaws, to prevent them. Various techniques and tools, such as STRIDE and Microsoft Threat Modeling Tool, can support the process. Best practices, such as involving all stakeholders and keeping models up to date, should be followed. With a proactive approach to security, organizations can protect their web applications and sensitive data.