As the adoption of cloud technology continues to surge, businesses are embracing its benefits by migrating their workloads from on-premises to the cloud. With the constant addition and expansion of workloads in the cloud, companies are faced with the challenge of managing and monitoring their security risks. The ever-evolving offerings and complexities of cloud providers further complicate this task.
Introduction
In this blog, we will dig into the world of ZeusCloud, a revolutionary open source cloud security platform that is transforming the way organizations protect their cloud infrastructure. You can join them as they explore the comprehensive features and functionalities of ZeusCloud, from uncovering attack paths and visualizing security findings to understanding user access and spotting critical misconfigurations. It will also highlight the platform’s customizability, streamlined remediation process, and compliance capabilities. Get ready to elevate the cloud security to new heights with ZeusCloud.
Zeus Cloud
ZeusCloud is a revolutionary open source cloud security platform designed to identify, prioritize, and resolve risks within your cloud infrastructure. Unlike other cloud security solutions that are complex, obscure, and demanding to configure, ZeusCloud offers a seamless experience that is both cost-effective and scalable as your cloud environment grows. With ZeusCloud, security, engineering, and devops teams gain access to valuable insights that empower them to concentrate on product development. The ultimate goal is to democratize security by providing every organization with a fundamental level of protection.
ZeusCloud Features
- Unveiling Attack Paths: Learn about the ways attackers can break into your system and find out which risks are the most dangerous when combined together.
- Embrace Graphical Context: See visual representations of security findings to better understand the context behind them and identify potential threats more easily.
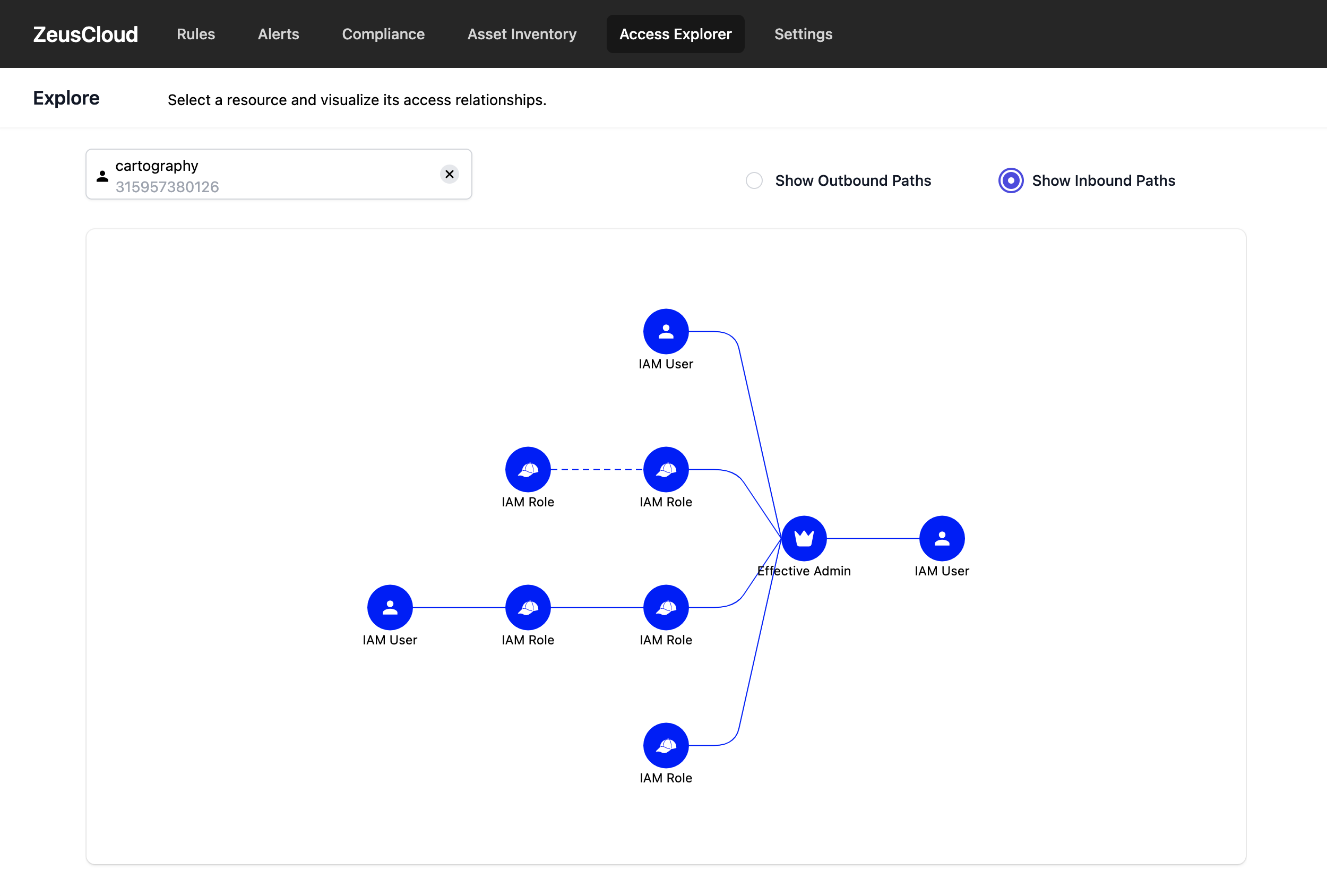
- Access Explorer: Use our visualization tool to understand who has access to different parts of your system. It shows you the web of permissions and privileges in an easy-to-understand way.
- Spotting Misconfigurations: Identify the most important misconfigurations that can be easily exploited by attackers. This helps you prioritize and fix them quickly.
- Customizability at Your Fingertips: Personalize the platform to meet your specific needs. Adjust security rules, mute alerts, and take advantage of other customizable features.
- Security as Code: Take charge of your security rules by modifying existing ones or creating new ones using our flexible approach. This allows you to adapt and customize your security settings.
- Streamlined Remediation: Follow our step-by-step guides to resolve security issues efficiently. They provide clear instructions for addressing each problem.
- Achieve Compliance: Ensure that your cloud infrastructure meets industry standards such as PCI DSS and CIS benchmarks to maintain regulatory compliance and establish a strong and secure cloud environment.
Deploy ZeusCloud Locally
$ git clone --recurse-submodules https://github.com/Zeus-Labs/ZeusCloud.git
$ cd ZeusCloud
$ make quick-deployVisit http://localhost:80 to access Zeuscloud.
AWS and ZeusCloud Connection
After successfully deploying ZeusCloud, the next crucial step is to establish a connection between the platform and your AWS account(s) for seamless scanning. Follow these simple instructions to effortlessly connect ZeusCloud to your desired AWS account(s):
Navigate to Settings > Add new account. Fill in the Account Name with whatever string-identifier you would like. Fill in remaining fields based on whether you are deploying with Option 1 or 2.
- Option 1: IAM role
- Select Named Profile for Connection Method. In the Profile dropdown, select the named profile you created earlier.
- Option 2: IAM user + access key
- Select User Access Key for Connection Method. Fill in the AWS Access Key ID and AWS Secret Access Key with the access key credentials you just created. Optionally, change the default region.
By following these steps diligently, you will establish a seamless connection between ZeusCloud and your AWS account(s), enabling comprehensive scanning and analysis of your cloud environment. Leverage the power of ZeusCloud to gain valuable insights into potential vulnerabilities and ensure the robust security of your AWS infrastructure.
Awaiting results
After successfully connecting your AWS account(s) to ZeusCloud, the platform will initiate a comprehensive scan, executing various security rules to assess the security posture of your accounts.
Please note that this scanning process may typically take between 10 to 15 minutes to complete. During this time, you can conveniently monitor the progress through two key sources:
- User Interface (UI): Access the Settings page within the ZeusCloud interface. Here, you will find a progress indicator displaying the percentage completed. This provides a visual representation of the scan’s advancement, allowing you to track the overall progress.
- Terminal Logs: Additionally, keep an eye on the terminal output as well. The cartography container will generate logs that provide real-time information about the ongoing scan. Monitoring these logs will offer deeper insights into the scan’s execution and any relevant findings.
Explore Findings
Once the scan is complete, you can delve into the insightful findings generated by ZeusCloud. To access these findings, follow these steps:
Navigate to the Alerts Tab: Head to the Alerts tab within the ZeusCloud interface. Here, you will discover a comprehensive overview of the identified security issues, encompassing misconfigurations and attack path-related concerns. These findings offer valuable insights into potential vulnerabilities within your environment.


Explore the Rules Tab: To gain deeper understanding, visit the Rules tab. This section presents a catalog of the specific security rules that were executed during the scan. By exploring this catalog, you can familiarize yourself with the rules applied and gain clarity on the security measures in place.
Access Explorer: Experience a comprehensive visualization of user access and permissions using our advanced IAM visualization engine.
Assess Compliance Posture: Additionally, ZeusCloud offers a dedicated Compliance tab. Here, you can evaluate your compliance posture across various frameworks. This feature allows you to ensure that your cloud infrastructure aligns with industry-standard frameworks, offering peace of mind and demonstrating your commitment to maintaining robust security practices.

Important Links
- Github Link: https://github.com/Zeus-Labs/ZeusCloud
- Website: https://www.zeuscloud.io/
- Sandbox Environment: https://demo.zeuscloud.io/
Conclusion
In conclusion, ZeusCloud is a game-changing open source cloud security platform that simplifies risk identification, resolution, and compliance in your cloud infrastructure. With its intuitive features, customizable security rules, and visual IAM engine, ZeusCloud empowers organizations to focus on product development while ensuring a strong security posture. By democratizing security and offering a cost-effective solution, ZeusCloud enables every organization to achieve a fundamental level of protection. Embrace ZeusCloud to revolutionize your cloud security and pave the way for a safer and more secure environment.




