In this blog, we explore top-tier reconnaissance tools that empower bug bounty hunters. From Shodan’s IoT device insights to Waymore’s web application vulnerability identification, each tool in this arsenal plays a vital role in securing the digital landscape. Join us on a journey through cyber reconnaissance, where these tools are the keys to unveiling the secrets of secure systems.
Introduction
Reconnaissance tools are essential for Bug Bounty Hunters, serving as a digital compass in navigating potential vulnerabilities. These tools efficiently gather information about a target, aiding hunters in identifying weak points before more intensive testing. By scanning and analyzing a target’s online presence, Recon tools empower hunters to uncover hidden entry points, exposed data, and potential attack vectors. This proactive approach maximizes the chances of discovering impactful bugs early in the process, crucial in the dynamic realm of cybersecurity. In the race against emerging threats, Recon tools are the linchpin for bug bounty success, providing hunters with a strategic imperative to excel in enhancing digital security.
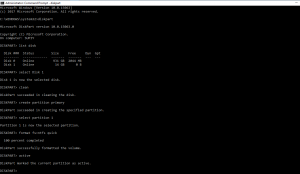
OSINT Framework
OSINT Framework is a collection of open-source tools and resources for open-source intelligence gathering. It is a centralized platform that consolidates various tools, websites, and data sources that help bug bounty hunters collect information about their target. This information can include email addresses, domains, subdomains, IP addresses, and more.
Bug bounty hunters can browse the OSINT Framework to access a wide range of tools and resources that can aid in discovering potential targets and gathering data on them. It is a valuable starting point for reconnaissance.
Shodan
Shodan is often referred to as the “search engine for the Internet of Things.” It allows users to search for Internet-connected devices and retrieve information about them, including open ports, services, banners, and vulnerabilities. Shodan is widely used for identifying exposed systems, IoT devices, and potential security risks.
Bug bounty hunters can use Shodan to find devices, such as webcams, servers, routers, or other networked devices, that may have weak security configurations or known vulnerabilities.
To search for devices with a specific keyword (e.g., Apache HTTP server), you can use:
shodan search "product:Citrix" --fields ip_str | awk '{print $1}'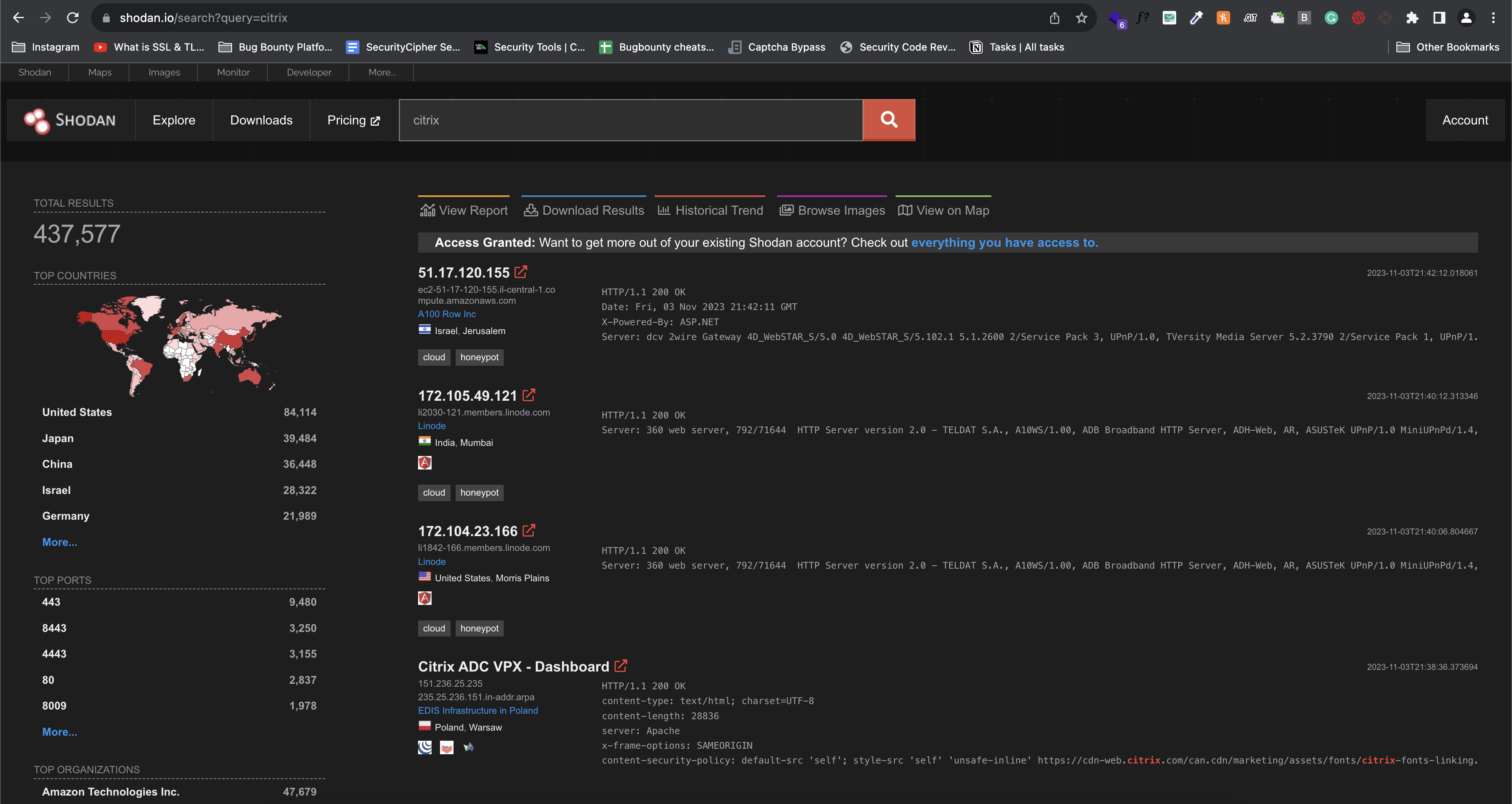
Censys
Censys is another search engine dedicated to Internet-connected devices. It provides detailed information about devices and services, such as certificates, SSL configurations, and banners. This information can be useful for asset discovery and vulnerability assessment.
Bug bounty hunters can utilize Censys to identify open services and examine SSL configurations to detect potential security issues. For instance, they can search for HTTPS servers with specific attributes to assess their security posture.
To search for Citrix , you can use:
censys search "citrix"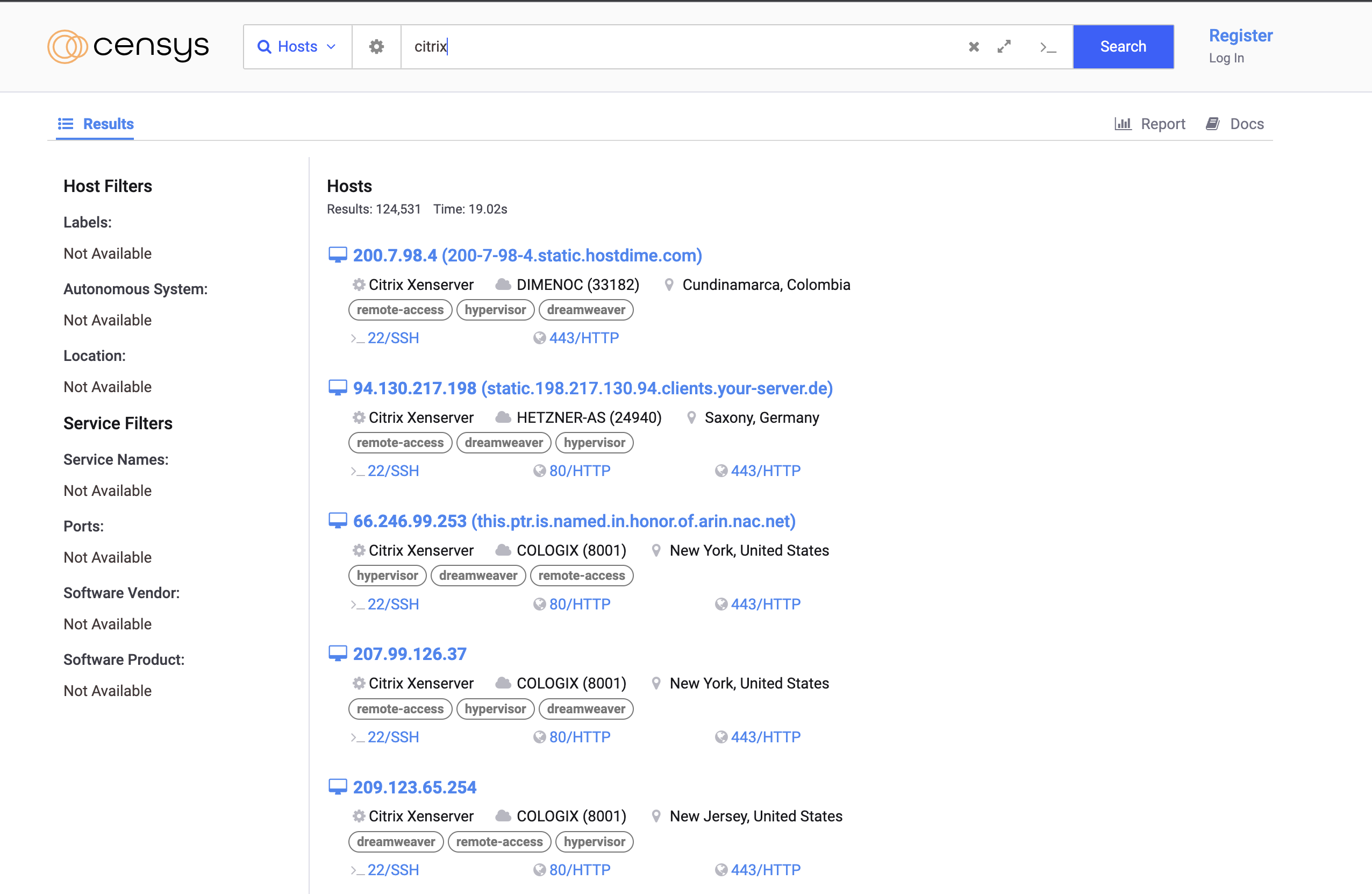
Subfinder
https://github.com/projectdiscovery/subfinder
Subfinder is a subdomain discovery tool that assists in finding subdomains associated with a target domain. Subdomains can often be overlooked and represent a broader attack surface for bug bounty hunters.
Bug bounty hunters can use Subfinder to discover subdomains of their target, potentially leading to the identification of hidden services or entry points. For instance, running Subfinder on “example.com” can reveal subdomains like “api.example.com” or “blog.example.com.”
To find subdomains for HackerOne, you can use:
subfinder -d hackerone.com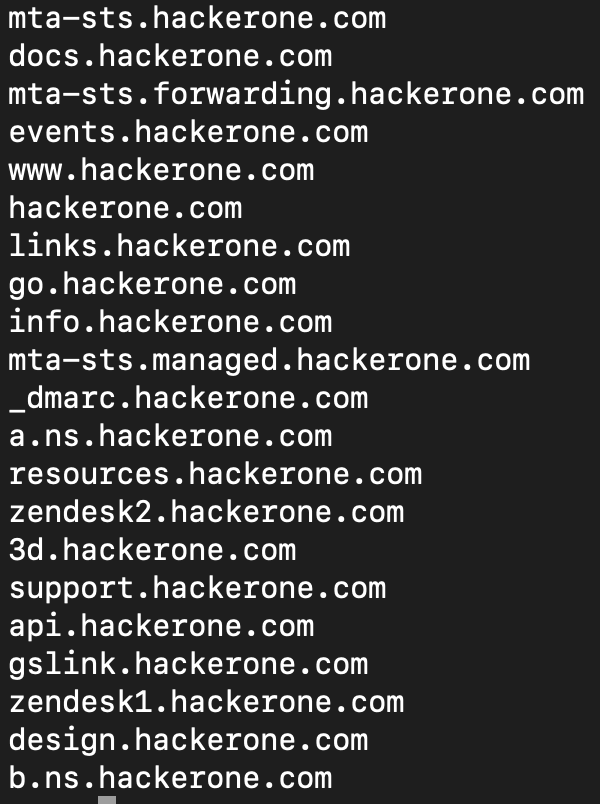
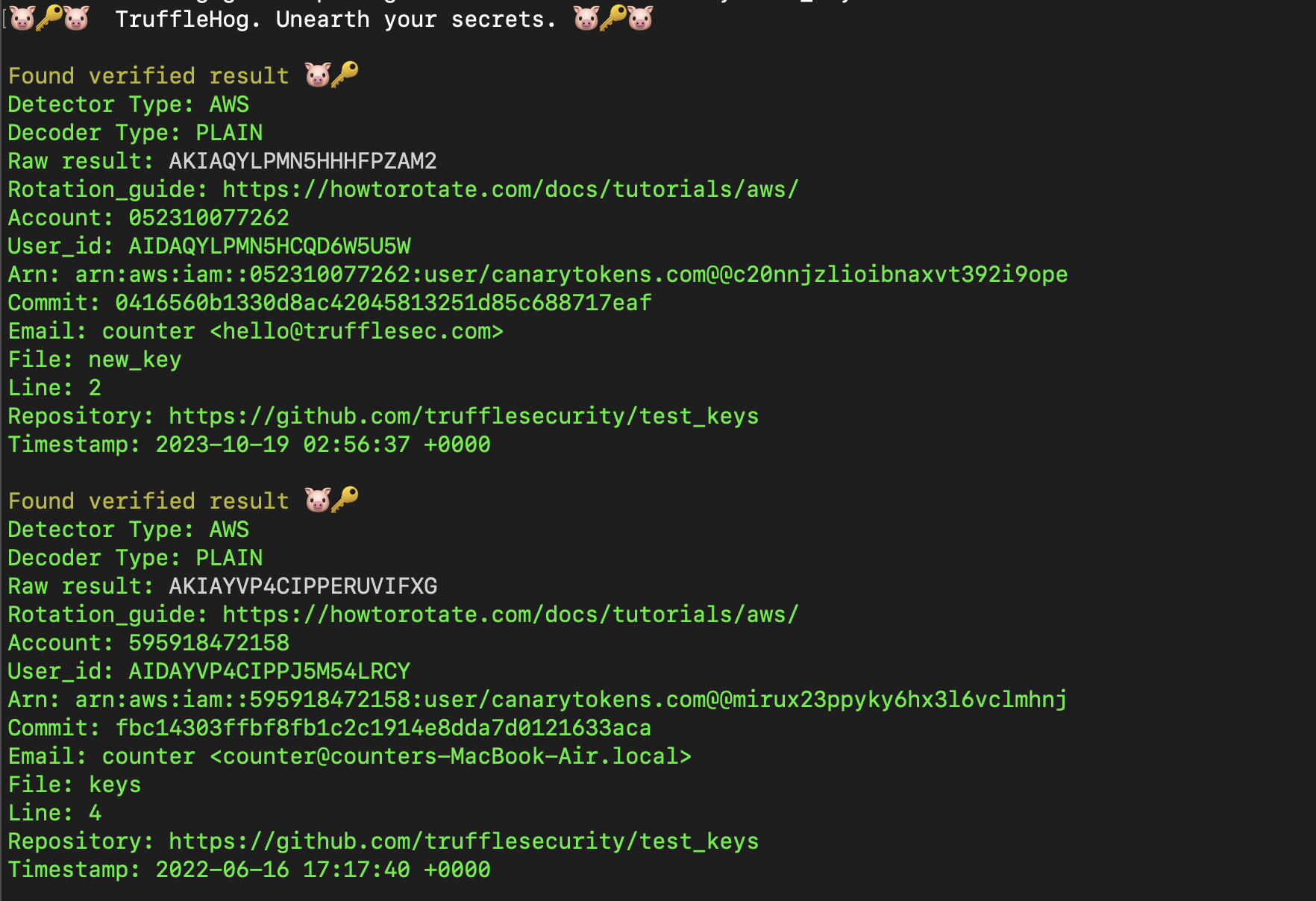
Trufflehog
https://github.com/trufflesecurity/trufflehog
Trufflehog is specifically designed for finding sensitive information, such as API keys, passwords, and other secrets, within code repositories. It scans code for high-entropy strings and known secret patterns.
Bug bounty hunters can use Trufflehog to scan code repositories for unintentional secrets or sensitive information leaks. For example, running Trufflehog on a Git repository URL can reveal accidentally committed secrets.
To scan a Git repository for secrets, use: trufflehog https://github.com/user/repo.git.
trufflehog git https://github.com/trufflesecurity/test_keysNmap
Nmap, short for Network Mapper, is a comprehensive network scanning tool used for network discovery and security auditing. It enables bug bounty hunters to identify open ports and services on target systems, providing insights into the network configuration.
Bug bounty hunters often use Nmap to perform port scans on target IP addresses or domains. For instance, running an Nmap scan on “example.com” can identify open ports and the services associated with them.
To scan a target host for open ports, use:
nmap -p 1-1000 example.com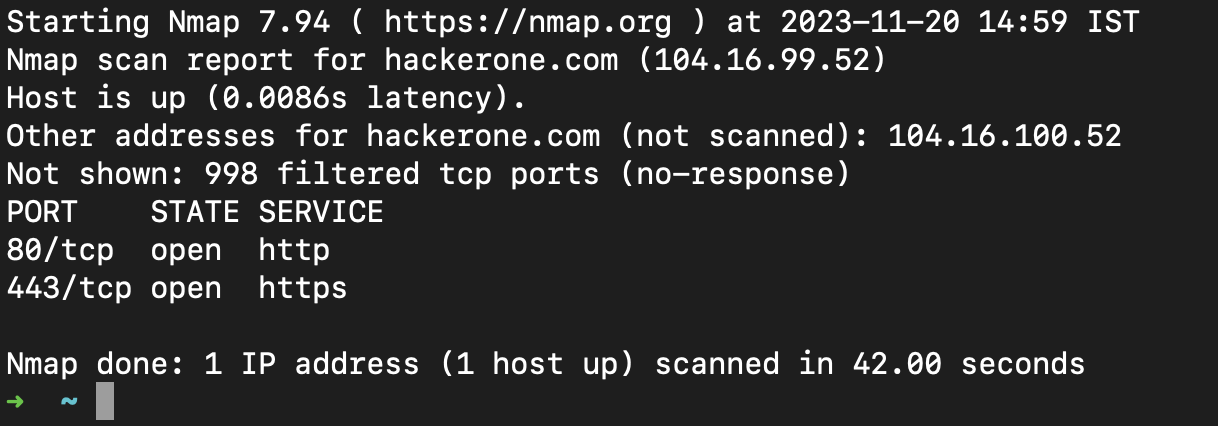
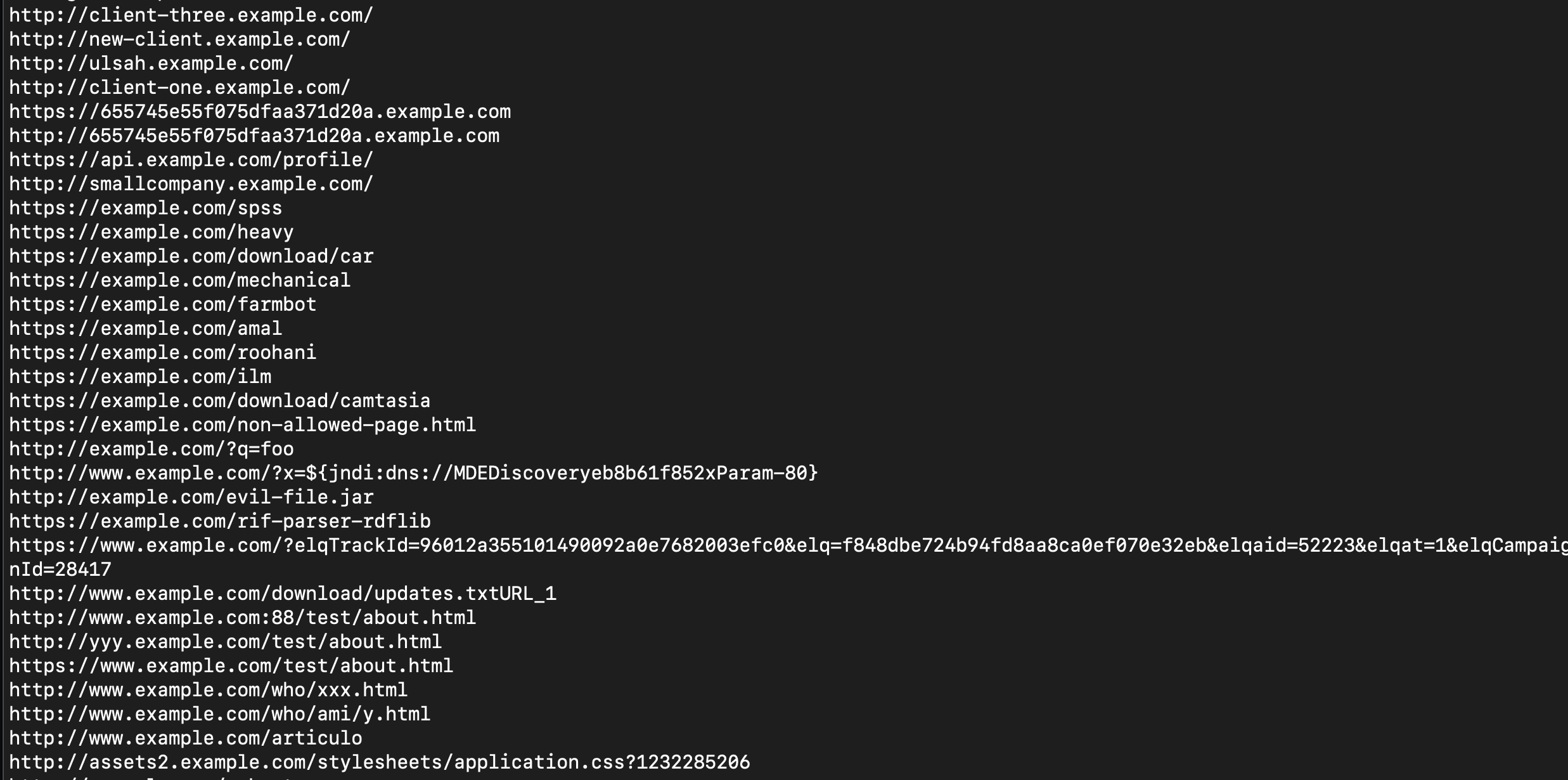
Waymore
https://github.com/xnl-h4ck3r/waymore
Anyone who does bug bounty will have likely used the amazing waybackurls by @TomNomNom’s. This tool gets URLs from web.archive.org and additional links (if any) from one of the index collections on index.commoncrawl.org. You would have also likely used the amazing gau by @hacker_ which also finds URL’s from wayback archive, Common Crawl, but also from Alien Vault and URLScan. Now waymore gets URL’s from ALL of those sources too (with ability to filter more to get what you want):
- Wayback Machine (web.archive.org)
- Common Crawl (index.commoncrawl.org)
- Alien Vault OTX (otx.alienvault.com)
- URLScan (urlscan.io)
Bug bounty hunters can use Waymore to gather extensive information about a target’s web presence.
Just get the URLs from all sources for redbull.com (-mode U is just for URLs, so no responses are downloaded):
python3 waymore.py -i redbull.com -mode U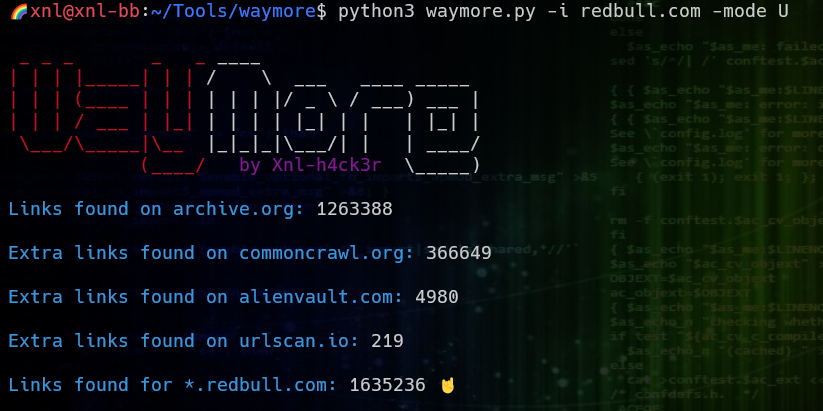
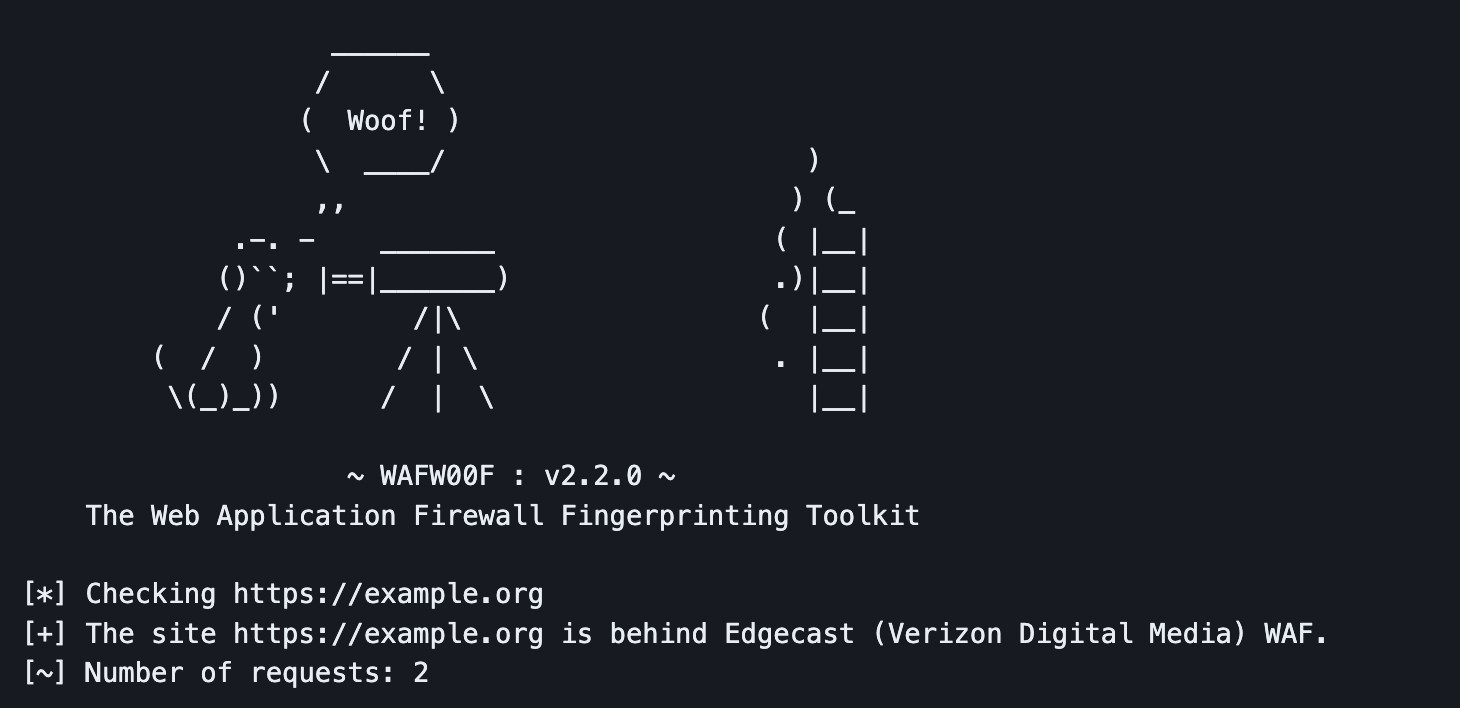
Waf00f
https://github.com/EnableSecurity/wafw00f
Waf00f is a simple tool that helps bug bounty hunters identify and fingerprint web application firewalls (WAFs) used by target websites. Understanding the presence of a WAF is crucial for security assessments.
Bug bounty hunters can use Waf00f to determine if a target website is protected by a WAF. For example, running Waf00f against “example.com” can reveal the type of WAF in use, which is essential information for bypassing or evading security mechanisms.
To check if a website uses a WAF, use:
wafw00f https://example.orgAmass
https://github.com/owasp-amass/amass
Amass is a powerful reconnaissance tool that integrates various subdomain enumeration techniques, DNS information gathering, and network mapping to provide a comprehensive view of a target’s online presence. It aims to discover as many subdomains and related assets as possible.
Bug bounty hunters can utilize Amass to identify subdomains associated with a target domain. This expanded scope can help in identifying potential attack surfaces and unexplored areas of the target’s infrastructure.
To discover subdomains for a domain, use:
amass enum -d example.com
FFuF
ffuf (Fuzz Faster U Fool) is a fast web fuzzer used for finding hidden resources and potential vulnerabilities in web applications. It is particularly effective for directory and file brute force discovery, helping bug bounty hunters uncover hidden or forgotten endpoints.
Bug bounty hunters can use ffuf to scan web applications for hidden directories and files by specifying a target URL and using a wordlist for brute force. For example, scanning “example.com” with a custom wordlist can reveal hidden resources.
To brute-force directories on a website, use:
ffuf -u https://example.com/FUZZ -w wordlist.txt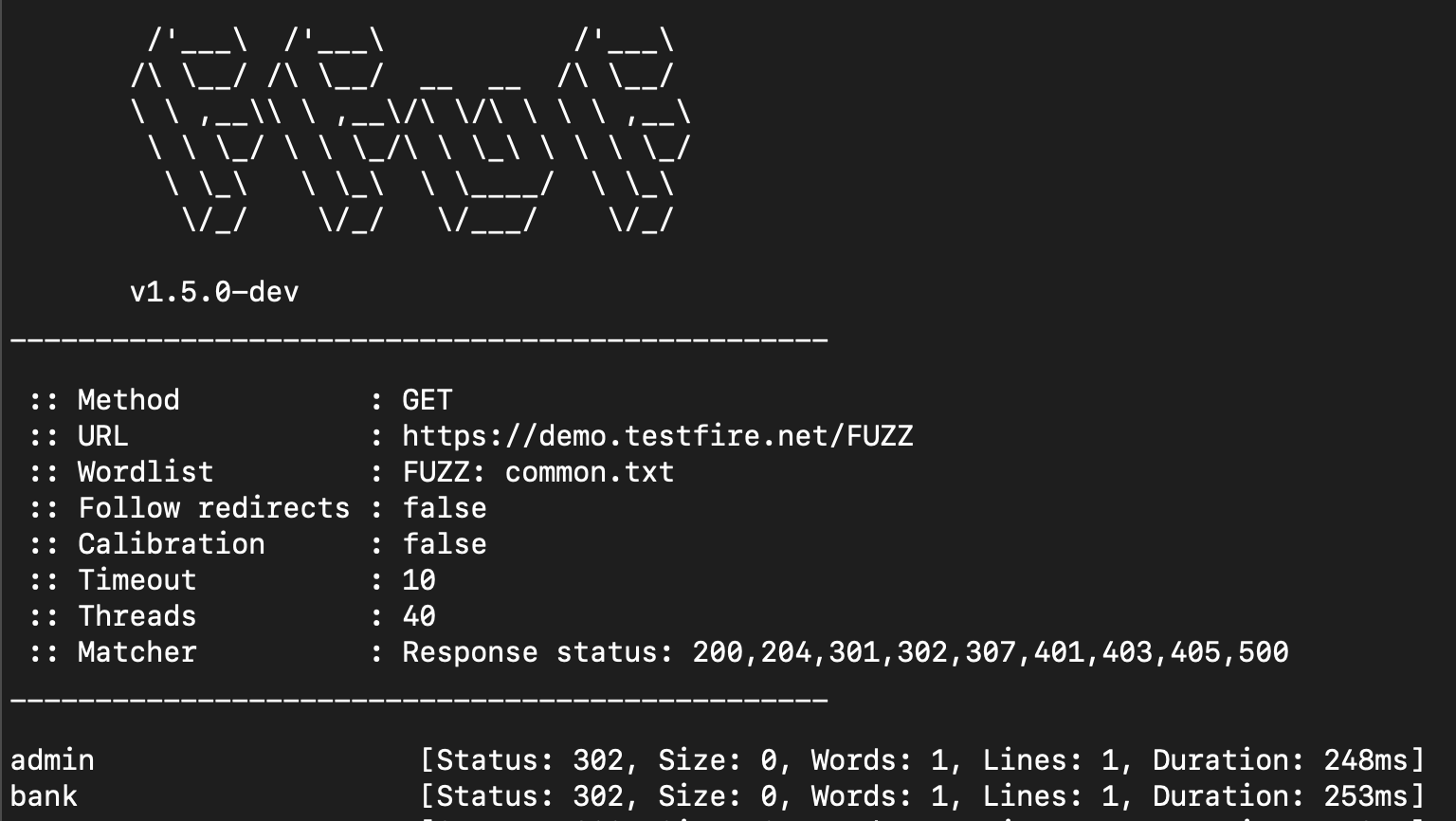
Waybackurl
https://github.com/tomnomnom/waybackurls
Waybackurl queries the Wayback Machine’s archive to retrieve historical snapshots of web pages. This tool is valuable for bug bounty hunters when they need to review historical content, track changes, and investigate the evolution of a website.
Bug bounty hunters can use Waybackurl to retrieve historical URLs and content snapshots for a target domain. By examining historical data, they may uncover deprecated functionalities or vulnerabilities that were previously exposed.
to retrieve historical URLs for a target domain, use:
waybackurl example.comtheHarvester
https://github.com/laramies/theHarvester
theHarvester is a reconnaissance tool designed for gathering information about a target through public data sources, search engines, and online resources. It focuses on retrieving email addresses, subdomains, and more.
Bug bounty hunters can use theHarvester to collect information about a target, such as email addresses associated with the domain or subdomains. For instance, running theHarvester on “example.com” with the “all” option can provide a wide range of data sources and results.
To get information related to a domain , use:
theHarvester -d example.com -l 100 -b all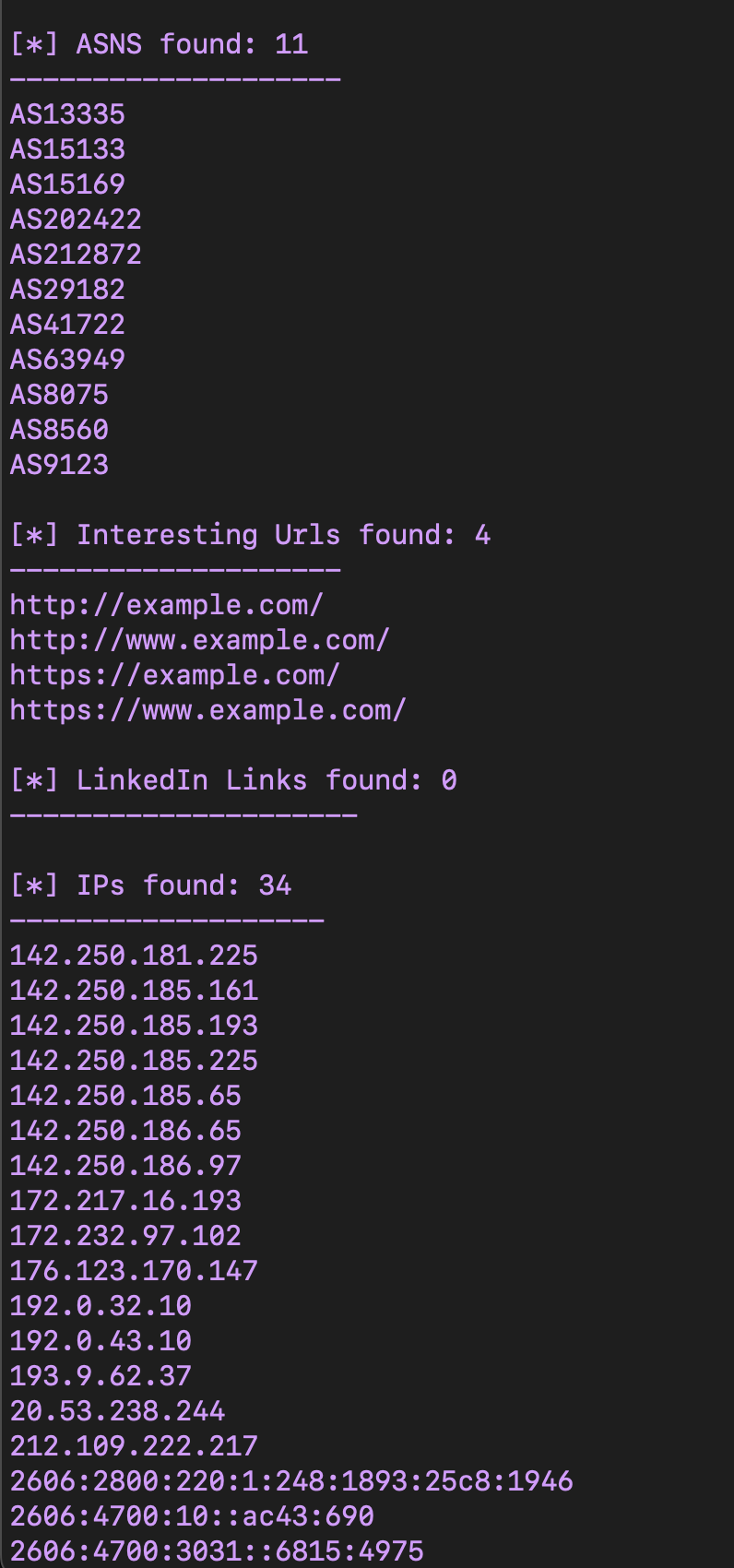
Google Dork
Google Dorking refers to the practice of using specific search queries on search engines like Google to discover hidden or sensitive information on websites. It is a manual technique for reconnaissance that can uncover files, directories, or information not intended for public access.
Bug bounty hunters can employ Google Dorking to identify specific vulnerabilities or information disclosure issues. For example, searching for PDF files containing the keyword “confidential”
A Google Dork for finding PDF files containing “confidential” in their titles:
filetype:pdf intitle:confidential site:example.com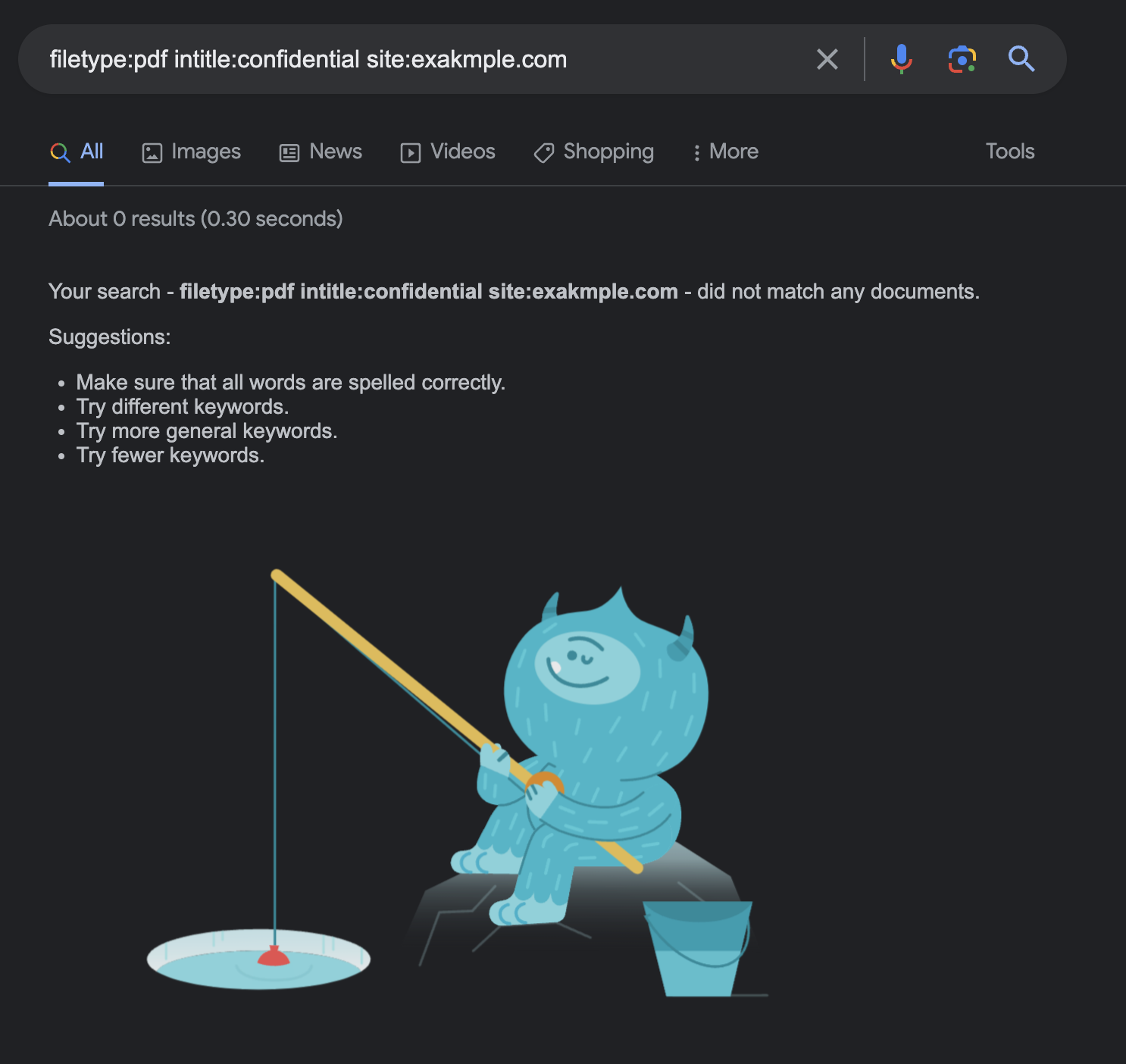
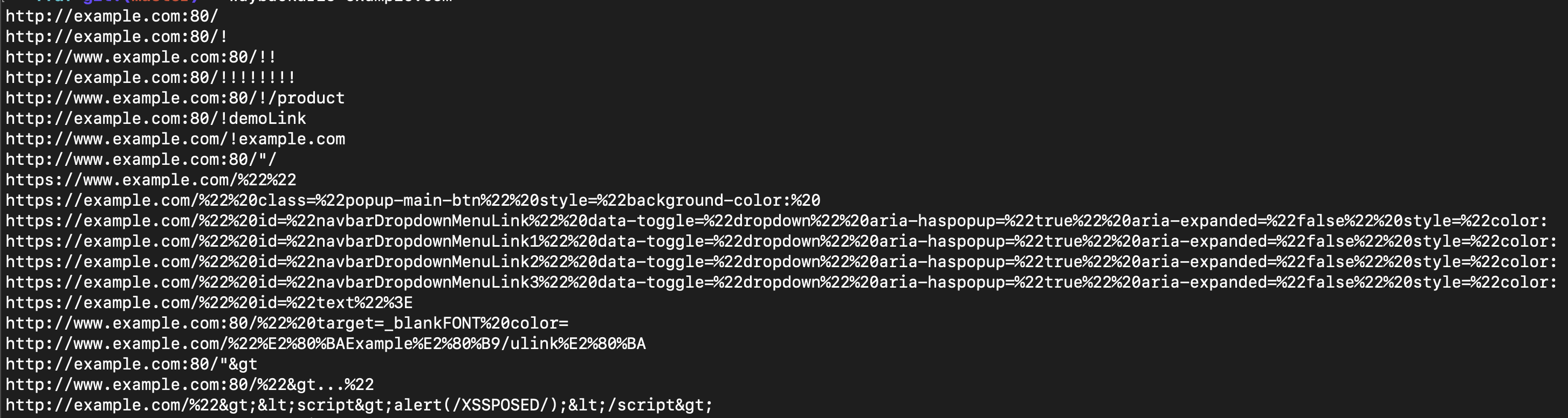
Gau
Gau, short for Get All URLs, is a versatile tool used for extracting URLs from a website or domain, including subdomains and paths. It offers an efficient way to enumerate web resources, helping bug bounty hunters discover hidden pages and endpoints.
Bug bounty hunters can use Gau to gather URLs associated with a target domain, which may include subdomains and specific paths. Gau is especially useful for expanding the attack surface. For example, running Gau on “example.com” can yield a list of URLs like “https://example.com/page1” and “https://subdomain.example.com/page2.”
To fetch URLs from a website, use:
gau example.comGitHub Dork
GitHub Dorking involves using specific search queries on GitHub to uncover repositories, files, or sensitive information that may have been unintentionally exposed. Bug bounty hunters can utilize GitHub Dorks to identify security vulnerabilities, exposed API keys, or other confidential information.
For instance, searching for configuration files that may contain sensitive information:
path:**/.env MAIL_HOST=smtp.gmail.com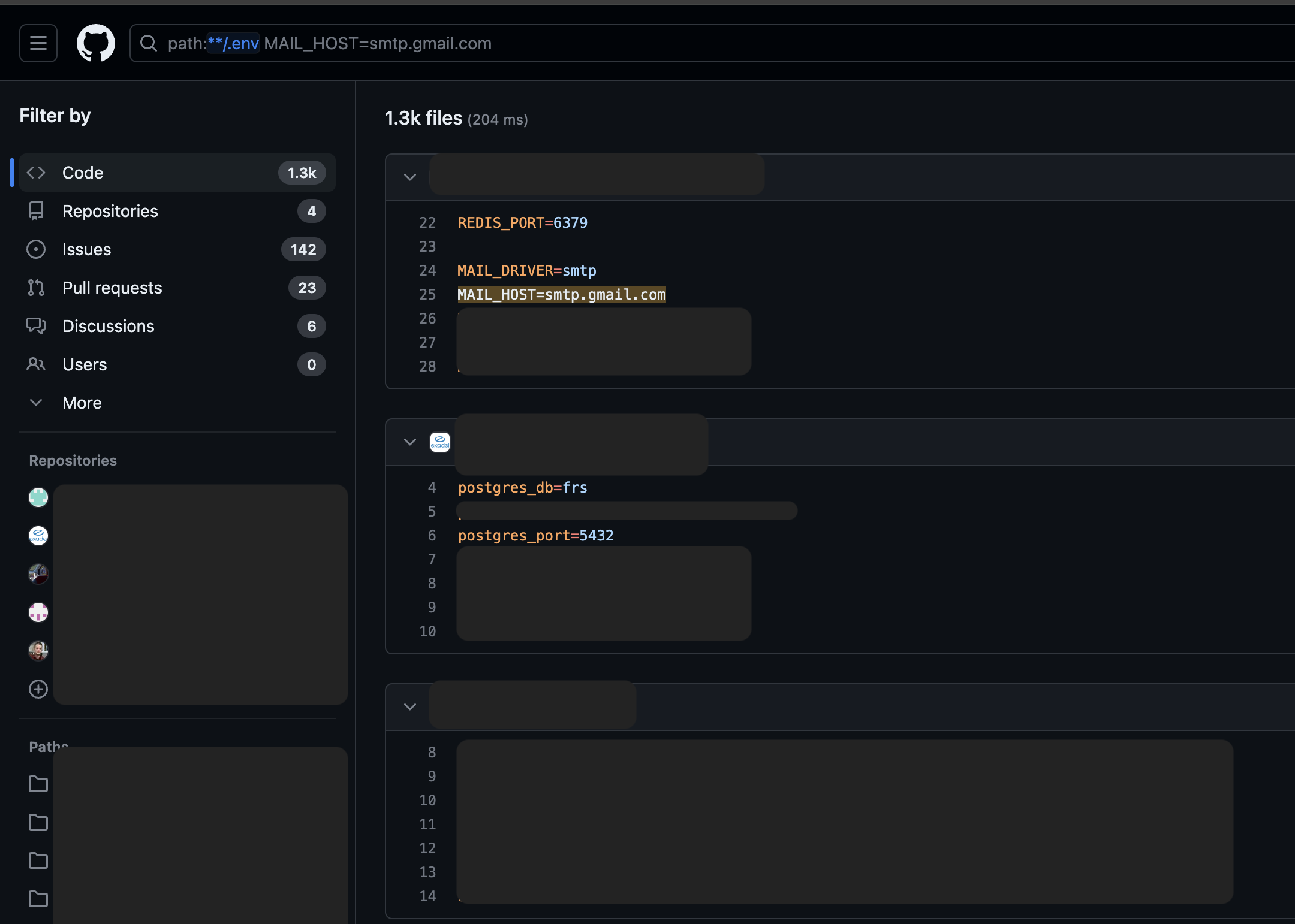
Conclusion
In the realm of bug bounty hunting, mastering the art of reconnaissance is non-negotiable, and the arsenal of top-tier tools explored in this blog stands as a testament to its importance. From OSINT Framework’s comprehensive intelligence gathering to Shodan’s IoT device insights and Waymore’s prowess in web application vulnerability identification, each tool serves as a key to unlocking the secrets of secure systems. As bug bounty hunters embark on their cyber journey, these reconnaissance tools act as the guiding light, enabling them to navigate through the vast digital landscape with precision. By leveraging these tools, hunters not only identify potential targets but also gain a deeper understanding of vulnerabilities, empowering them to report impactful bugs and contribute significantly to the enhancement of digital security. The secrets are out there, and with these reconnaissance tools in hand, bug bounty hunters are well-equipped to uncover and address them, one vulnerability at a time. Join us in embracing the power of cyber reconnaissance, where knowledge is the key to securing the ever-evolving digital frontier.