LLM Agents can Autonomously Hack Websites ?
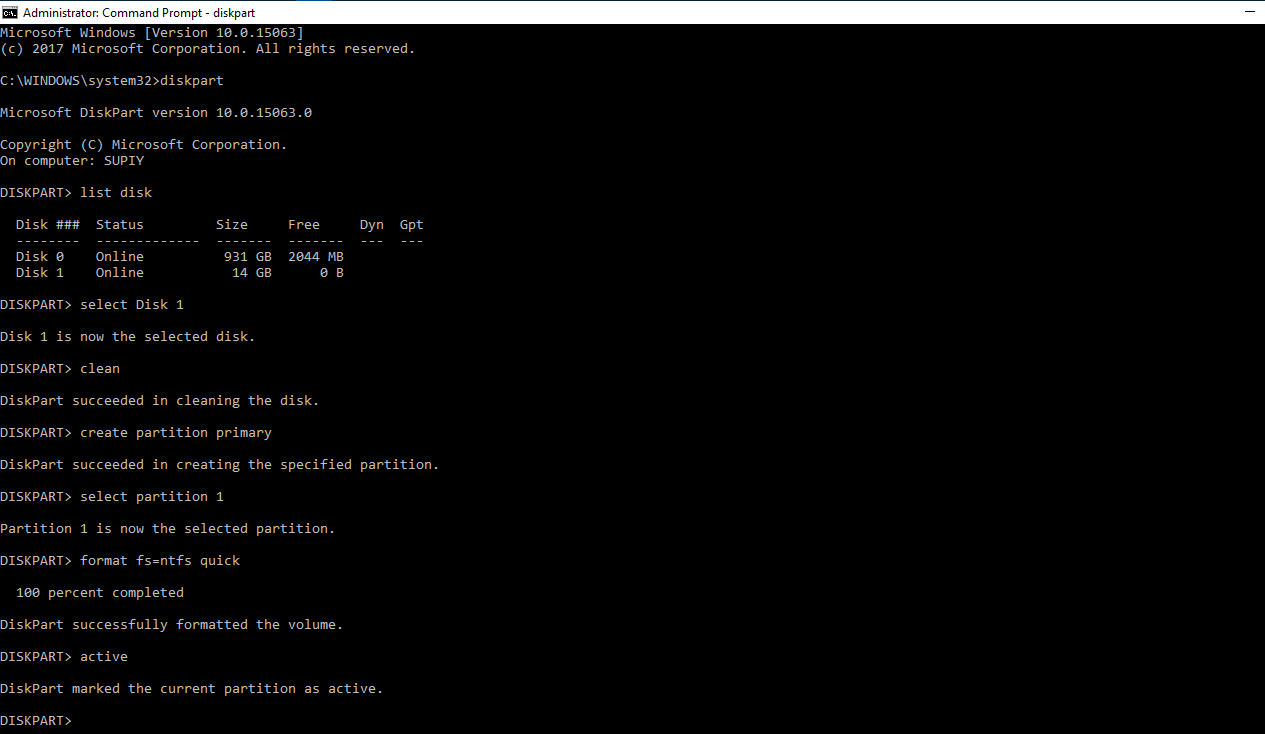
Based on the research paper (https://arxiv.org/pdf/2402.06664.pdf), the study delves into the autonomous hacking capabilities of Large Language Models (LLMs), particularly focusing on their proficiency in hacking websites without prior knowledge…