This article is a part of the Guide for Burp Suite series. Within the previous article, we learn about some of the features of the Dashboard tab. Now we’ll move forward and see some of the features of the Target Tab. So Let’s Get Started.
The Target tab contains the site map, with detailed information about your target applications. It lets you define which targets are in scope for your current work and also lets you drive the process of testing for vulnerabilities. Looking more closely at the Target tab, you will notice there are three subtabs available: Site map, Scope, and Issue Definition.
1. Site map
You will see many websites on the site map. As you browse the applications in the browser, Burp creates a site map of all the browsed applications. Click on the Target tab, and then Site map, to view the site map. The site map contains all of the URLs you have visited in your browser. It shows you a tree view that contains a hierarchical representation of content, with URLs broken down into domains, directories, files, and parameterized requests. You can expand any branches to see further detail.
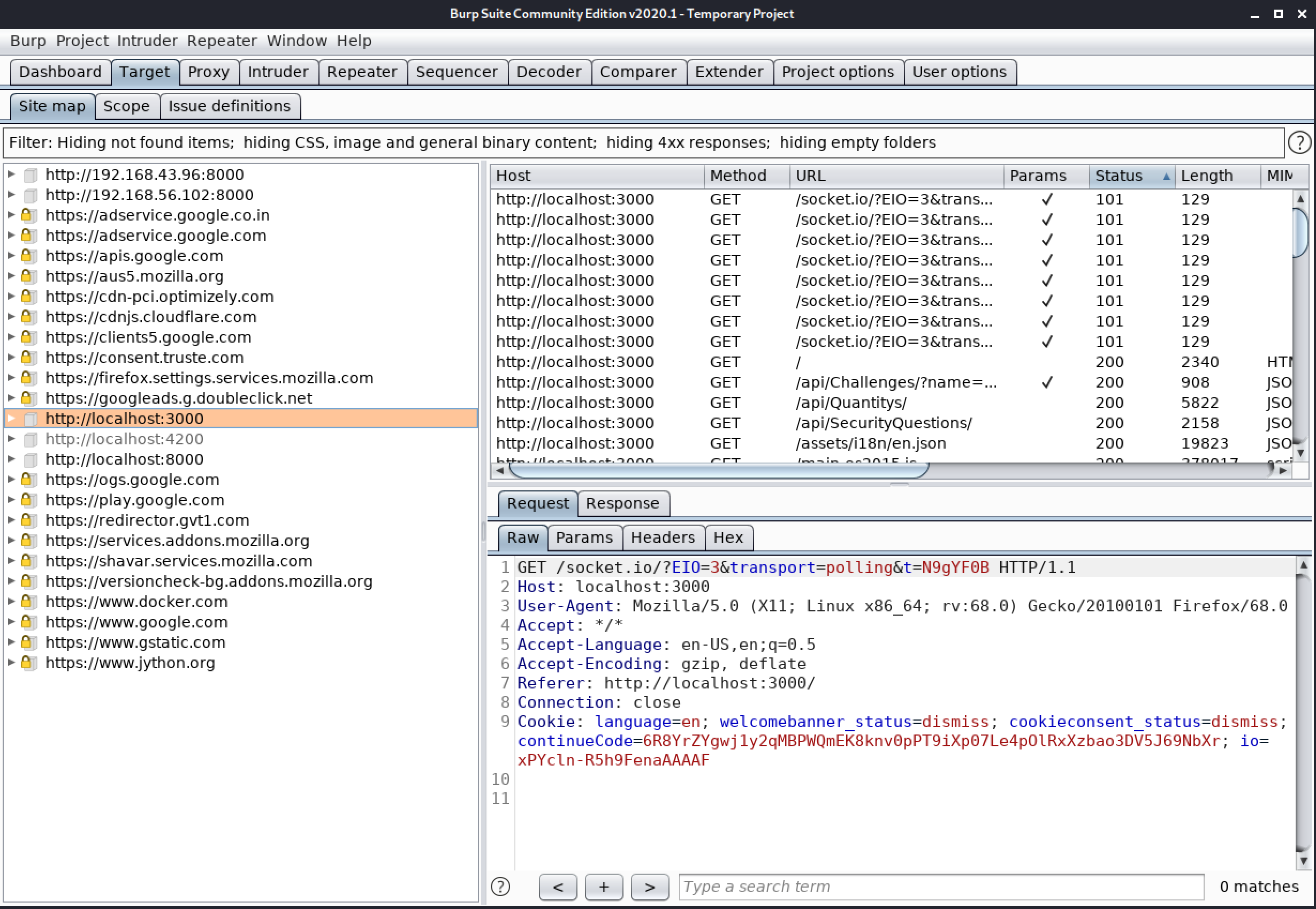
Display Filter Feature
The site map has a display filter that can be used to hide some of its content from view, to make it easier to analyze and work on the content you are interested in.
Clicking on the filter bar opens the filter options for editing. You can configure some of the filters on the basics of the following attributes.
- Request type – You can select if you want to show/hide only in-scope items, only requested items, only requests with parameters, or you can hide not-found items.
- MIME-type – You can select if you want to show/hide responses containing various different MIME types, such as HTML, Script, XML, CSS, Images, Flash, Other text, or Other binary.
- Status code – You can select if you want to show/hide responses with various HTTP status codes such as 2xx, 3xx, 4xx, or 5xx.
- Folders – You can optionally hide empty folders in the tree view. It will hide all the folders which are empty.
- Search term – You can search for a specific keyword. You can select whether the search term is a Case sensitive or a Regex. If you select the “Negative search” option, then only items not matching the search term will be shown.
- File extension – You can choose which file extensions you want to show or hide.
- Annotation – You can choose that if you want to show items with are commented or highlighted.

Add/remove target form scope
These options create new target scope rules which add or remove the selected item from the scope. A common technique when testing an application that includes some sensitive URLs is to add the whole application path (domain or directory) to the target scope, and then select the sensitive items and exclude them from the scope.

Scan
After selecting this option a new Scan window will open and there you can set up a new scan for the selected target.
Engagement tools
- Search – You can use the search functionality to search the selected branch of the site map for items matching a specific expression/keyword.
- Find comments/scripts – You can use the Find comments/scripts functionality to search the selected branch of the site map for comments and scripts.
- Find references – You can use the Find references functionality to search all of Burp’s tools for HTTP responses that link to the selected item.
- Analyze target – You can use the Target Analyzer functionality to analyze the selected branch(es) of the site map and tell you how many static and dynamic URLs it contains, and how many parameters each URL takes.
- Discover content – You can use the Discover content functionality to discover content and functionality that is not linked from visible content that you can browse to or spider.
- Schedule task – You can use the Schedule task functionality to create tasks that will run automatically at defined times and intervals.
- Generate CSRF PoC – You can use the Generate CSRF PoC functionality to create some HTML which, when viewed in a browser, will cause the selected request to be issued.
- Simulate manual testing – The Manual testing simulator can be used to generate HTTP traffic that is similar to that caused by manual penetration testing.

2. Scope
This tab contains the information of in-scope or out-of-scope URL’s. If you are testing an application then you can enter the application’s URL in the “Include in scope” by clicking on the “Add” button.

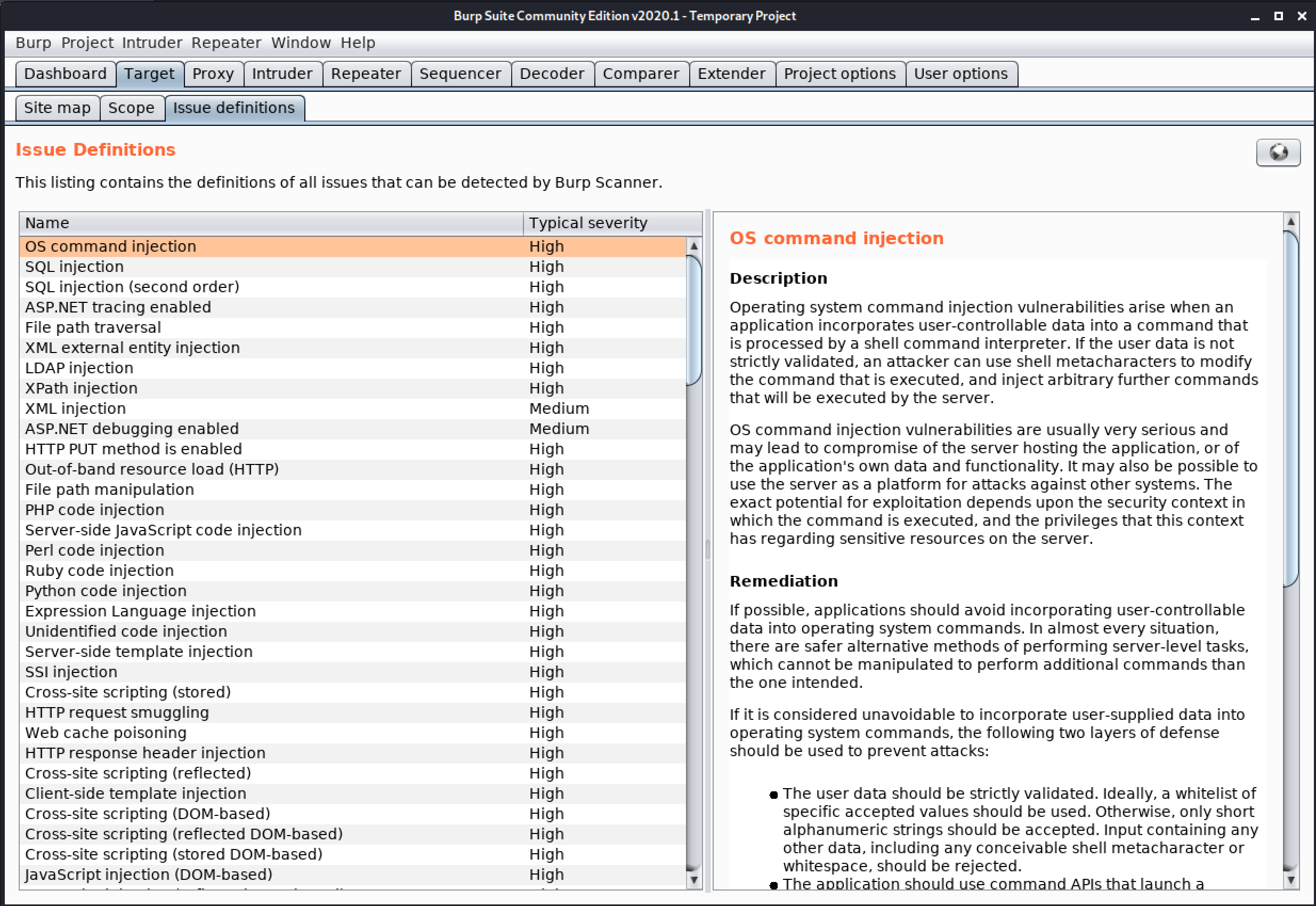
3. Issue Definition
This tab contains the listing of definitions of all the issues that can be detected by Burp Scanner.
Congratulation! finally, you know about the Target tab which is present in the Burp Suite. In the next Part, we will discuss the Proxy tab.
#burpsuite #burpsuitetutorial #burp #webapplicaitonpentesting