This article is a part of the Guide for Burp Suite series. Within the previous article, we learn about some of the features of the Proxy tab. Now we’ll move forward and see how to work with the Burp Proxy tab. So Let’s Get Started.
Burp Proxy lies at the heart of Burp’s user-driven workflow, and lets you intercept, view, and modify all requests and responses passing between your browser and destination web servers. For all the Practical we will be using OWASP Juice Shop which is running on a docker in Kali Linux.
Working with Burp Proxy
The following are the steps you can go through to listen to all HTTP/HTTPS traffic using the Burp Proxy.
1. Open the Firefox browser and enable the network proxy from the “Foxyproxy” extension.
2. In Burp, go to the “Proxy” Intercept tab, and ensure that “Interception is on”.

3. In the Firefox browser, visit any URL on OWASP Juice Shop.
4. In Burp, go to the “Proxy” -> “Intercept” tab. Now you can see your browser’s request displayed in plain text for you to view or edit.
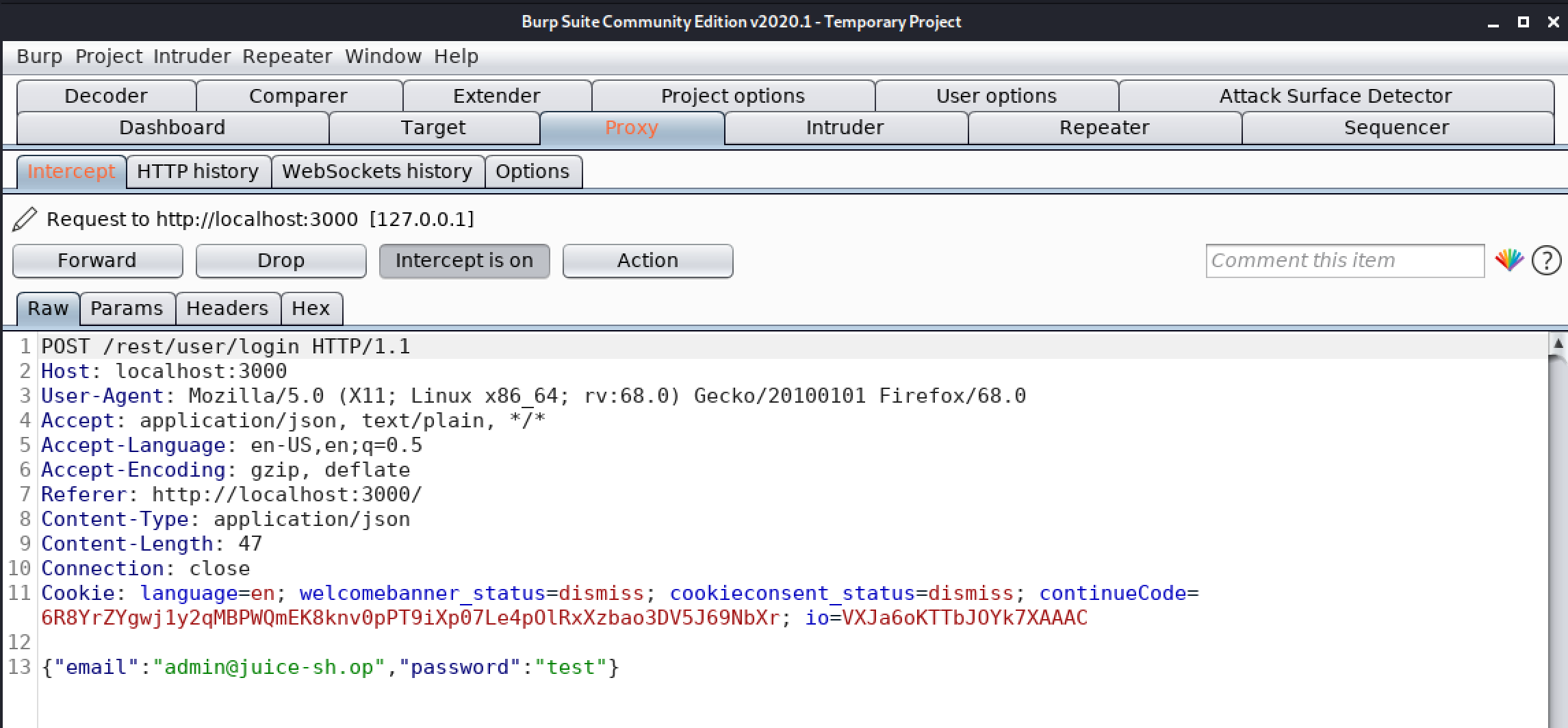
5. Click on the “Forward” button to send the request to the server. Normally, your browser will send many requests in order to display the page. Look at each request and then forward it to the server.
6. Go to the “Proxy” -> “HTTP History” tab. This contains all the HTTP requests and responses that have passed through the Proxy Tab. Select any request, and look at the HTTP request and response. If you want to make any changes in the request then you can send the request to “Repeater” for any further modifications.

Congratulations! finally, we know how to work on the Burp Proxy tab. In the next Part, we will discuss the Intruder tab.
#burpsuite #burpsuitetutorial #burp #webapplicaitonpentesting